Crack Excel Password Mac Os X
'I forgot my login password for my MacBook and I'm not sure if the username is correct. So can anyone help me reset Mac login password? Thanks in advance.' It really happened to everyone at some point – you create a new password and don't remember to save it somewhere, and then before you know it you've forgotten what it was.
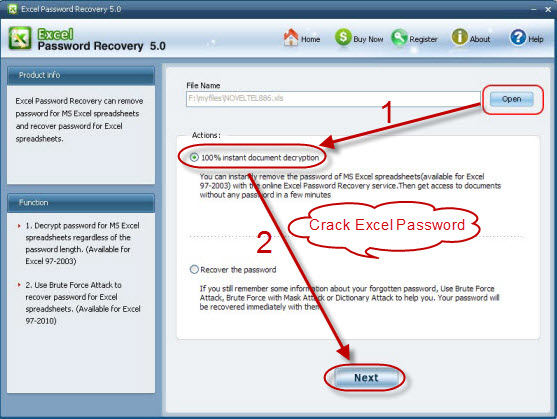

Have you forgotten your Excel password for a workbook or sheet? Or has someone left your office and they forgot to unlock an Excel workbook with a password. Whilst Mac OS X is based on a Unix variant BSDthere are several key differences between traditional Unix-based and Mac OS systems when it comes to password storage. Crack excel password mac os x Preflight Locate, modify, or remove PDF elements using customizable fixup profiles. Having created Mac OS X login password but forgot it unfortunately? So can anyone help me reset Mac login password? Excel, ppt, accesss office files password.
So forgot your Mac OS X login password? You are not out of luck. You will need to reset your forgotten Mac password and there are several ways to do this. Virtual Piano Keyboard Linux. We'll focus on the two best methods to recover login password for Mac computer (MacBook Pro, iMac, MacBook Air, Mac Pro, etc. Which are running Mac OS X 10.9, 10.8, 10.7 and lower). Check them now.
Way 1: Reset Lost Mac Login Password with Apple ID This one must be the best approach for Mac OS X (Mavericks, Mountain Lion, Lion etc) users because it's extremely fast and simple. The only requirements are that you must have tied an Apple ID to a user account, and you must have internet access so that the Mac can contact Apple to initiate the reset procedure. Follow the instruction to reset lost Mac login password. • From the Mac login or boot screen, enter any wrong password three times to summon the 'Password Hint' box and a message saying 'If you forgot your password you can reset it using your Apple ID'. Click on that (>) arrow icon to start the Apple ID based reset.
• Enter your Apple ID credentials, this is the same information used to log into the App Store, iTunes, and iCloud, then click 'Reset Password'. • Follow the instruction to enter a new password. Confirm the new password and let the Mac boot as usual.
Way 2: Reset Your Forgotten Mac Login Password with Install Disk The other method is to use your installation disk of OS X. If you don't have this disk, then you'd better to buy a copy of Mac OS X. After all things set up, you can follow the steps to finish your reset procedure. • Put your Mac OS X disk into the drive.
Once you have booted off the disk you will need to choose your language, and then OS X will prepare the installation environment. • Then choose the 'Utilities' menu and choose 'Reset Password'. • Now you need to choose the volume with the account you need to change the password for, choose the account from the drop down, and generate your new password and password hint if you wish to use one.
OS X 10.5 (Leopard) + OS X 10.6 (Snow Leopard) First find a users' GUID: dscl localhost -read /Search/Users/username grep GeneratedUID cut -c15- After getting the GUID you can dump various hashes. By default the only hash stored is the salted SHA1. If the user has turned on SMB file sharing then the NTLM hash will also be stored.
If you upgraded from 10.3->10.4->10.5 then the zero salted SHA1 is also stored. Salted SHA1 (first 8 characters are the salt) cat /var/db/shadow/hash/GUID cut -c105-152 Zero-Salted SHA1 (first 8 characters are the salt and will always be all zeros) cat /var/db/shadow/hash/GUID cut -c169-216 NTLM (first 32 characters are NT, next 32 are LM) cat /var/db/shadow/hash/GUID cut -c-64. OS X 10.8 (Mountain) & 10.9 (Mavericks) & 10.10 (Yosemite) The shadow files are stored on the filesystem at /var/db/dslocal/nodes/Default/users/%user%.plist. They are in plist format so you'll need to use the plutil command to view them or use the defaults command to extract/write specific keys if desired. Only the root user has access to the files. To view the contents of a shadow file for a user: sudo plutil -p /var/db/dslocal/nodes/Default/users/%username%.plist To get the hash: sudo defaults read /var/db/dslocal/nodes/Default/users/%username%.plist ShadowHashData tr -dc 0-9a-f xxd -r -p plutil -convert xml1 - -o - Where%username% in the above example is the user you're looking for the hash for.
Finally the wanted hash starts with '$ml$' and length is 203 characters. Few links to help you: - - - to automate the process (.app).
Tool to automate these steps tool created in early 2011 is a password hash extractor & companion tool to John the Ripper. Sadly the development of this tool has been stopped (but could be forked.), the current status is: Dave compiles fine on Yosemite and will happily (but very slowly) crack user passwords. Out of the box, OS X uses PBKDF2 to encrypt its user passwords which is very slow to crack for one machine. Turning on Windows (SMB) file sharing will disable this feature. Github project page readme.